On April 25, 2025, the senior advisor to the acting Archivist of the United States (AOTUS) sent a memorandum to the heads of federal departments and agencies on the management responsibilities they have with respect to electronic messages that constitute public records.
In the memorandum (below), Jim Byron, Senior Advisor to Secretary Marco Rubio, Acting AOTUS, reminds agencies the obligation all officials have to memorialize official business conducted on a personal device or account by forwarding or copying an official account with the electronic correspondence.
Byron observes that “the use of the auto-delete function on digital messaging applications may prevent agency officials from meeting this critical obligation, possibly resulting in the permanent loss of federal records,” but this conflicts common sense.
The memorandum does not reference the March 25, 2025 guidance from the White House to staff at the U.S. DOGE Service, which is far clearer.
That policy emphasizes that “the basic rule is to preserve all work-related communications and records, regardless of format.”
Messages that constitute public business that are sent on personal devices and on Signal must be archived, which means any auto-delete feature in the app should be disabled, not enabled by default — including those in the chat Acting Archivist Rubio was on with the National Security Advisor.
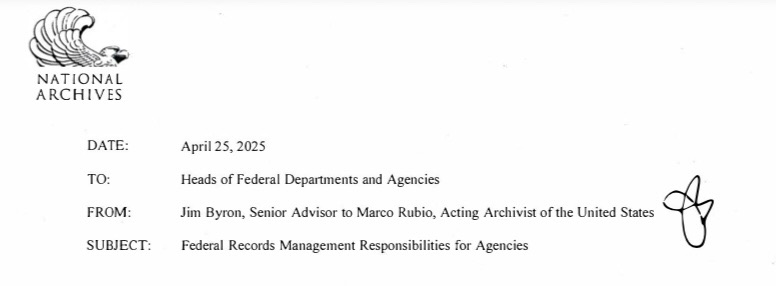
Federal Records Management Responsibilities for Agencies
Congratulations to all of you on your recent appointments to federal service.
I write to make you aware of resources that are available to you and your employees regarding records management in your agencies.
All federal employees create and manage records as an integral part of their responsibilities in performing agency missions. Federal records protect the rights and interests of the public, allow officials to be held accountable for their actions, and document our nation’s history. Also, good records management helps your agency operate more effectively and efficiently.
It is crucial agency heads work with their Senior Agency Official for Records Management and Agency Records Officers to communicate the importance of their records management responsibilities to all staff, including political appointees.
Together, federal agencies and the National Archives work toward government transparency, public engagement, and accountability by promoting our obligations under the Federal Records Act (FRA). The FRA, at 44 U.S.C. § 3101, charges you, as the agency head, with creating and preserving federal records containing adequate and proper documentation of the agency’s activities so that the legal and financial rights of the Government and individuals affected by the agency’s activities are protected.
The emergence of —and increasing reliance upon — new forms of electronic communication can make records management more challenging, but no less important. The FRA imposes strict requirements on the use of personal accounts to conduct agency business. If any agency employee uses a personal account to engage in official business, they must copy an official account or forward their message to an official account within 20 days. 44 U.S.C. § 2911.
The use of the auto-delete function on digital messaging applications may prevent agency officials from meeting this critical obligation, possibly resulting in the permanent loss of federal records.
It is thus vital that you ensure staff are properly trained on their FRA obligations. Agency heads must ensure that their records management programs provide effective control over the creation and maintenance of records, 44 U.S.C. § 3102, and safeguard against the removal or loss of records, 44 U.S.C. § 3105.
We encourage you to take prompt action to ensure that your recordkeeping policies are up-to-date, and that they adequately educate agency staff how to create, maintain, and dispose of federal records, especially when using third-party apps. Additional details about the appropriate maintenance of electronic records, including metadata retention requirements, can be located at 36 CFR Part 1236.
Questions related to FRA compliance may also arise when agencies transfer their functions to other agencies. Agencies must ensure that:
Paper and electronic records are properly identified and segregated from non-records, as those terms are defined by federal law;
Temporary paper and electronic records are only disposed of in accordance with a NARA-approved agency-specific or General Records Schedule; and
Paper and electronic records are transferred to another federal entity, inactive storage, or NARA only in accordance with the procedures outlined in 36 CFR Parts 123 | to 1235.
NARA will be issuing additional guidance and resources to assist agencies with fulfilling their records management responsibilities when consolidating and reorganizing.
Thank you for your attention to these matters. If you have any questions about your agency’s records management responsibilities or would like to discuss anything further, I invite you to contact William Fischer, Acting Chief Records Officer at NARA, at william.fischer@nara.gov.
cc
Senior Agency Officials for Records Management Agency Records Officers
General Counsels